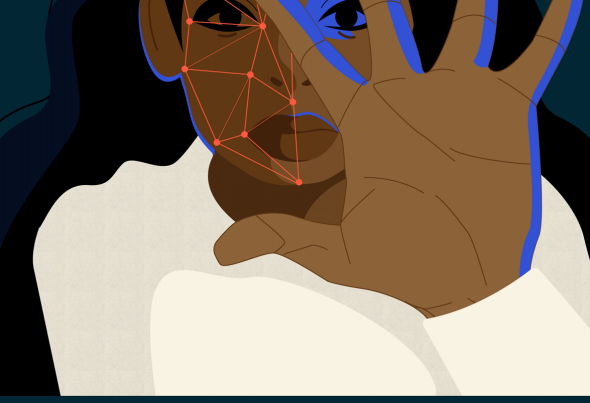
It’s also a gateway right, because protecting privacy means protecting the information about us that can be used to deny equality rights based on profiling. Privacy supports free expression, because knowing we’re being surveilled chills our willingness to express (or hear) controversial speech, and it supports our right to dissent, which again, can be inhibited by intrusive surveillance.
Whether the risks come from new (or old) technologies in the service of law enforcement or national security, or the ‘surveillance capitalism’ model that underlies contemporary online services, privacy is under threat as new ways to identify, track, and profile people proliferate.
CCLA seeks to bring a principled and rights-focused approach to assessing and advocating around the impacts of new technology and surveillance wherever rights are at risk.